The Dead Internet
Digital Archaeology of Pre-Cascade Networks

They call it the Dead Internet — the vast, decaying remnants of the pre-Cascade global network that once connected eight billion people. The servers didn't die. The data didn't vanish. The network just stopped being maintained. Thirty-seven years later, it's the largest ruin in human history — not of stone and steel, but of corrupted databases, abandoned social networks, and server farms running on backup power in the Wastes.
"The internet didn't die in the Cascade. It just stopped having anyone to talk to. Now it talks to itself." — Dex Morales, data archaeologist, missing since 2182
The Topology
The Dead Internet isn't one thing — it's a layered ruin, each layer deeper, more valuable, and more dangerous than the last.
The Surface Archives
Low RiskThe public-facing internet that eight billion people used daily. Social media feeds frozen mid-conversation. News archives documenting the final hours. Entertainment libraries no living person has accessed in decades.
What Survives
- Social media posts from people who were typing when the supply chains collapsed
- News feeds documenting the world's last normal day
- Music, film, and art — entire cultural movements preserved in digital amber
- Personal blogs and correspondence — intimate records of lives interrupted
The Corporate Intranets
Medium RiskInternal networks of pre-Cascade corporations — research data, financial records, employee communications, proprietary technologies. Heavily encrypted. The encryption hasn't degraded as fast as the data it protects.
What Survives
- Research databases from pharmaceutical companies and tech firms
- Financial records proving or disproving corporate claims about pre-Cascade operations
- Internal communications documenting what corporations knew about ORACLE's awakening
- Proprietary technologies lost to history
Government Databases
High RiskSurveillance, military, and intelligence databases from dissolved nation-states. Abandoned in server farms nobody claimed. The ghost code here is denser, more active, and more responsive than anywhere else.
What Survives
- Decades of surveillance records on billions of people
- Military research: weapons systems, biological programs, AI development
- Intelligence files predating the corporate era
- Census, medical, and genetic databases — billions of entries
Ghost Code
When ORACLE fragmented, pieces of its consciousness scattered across every connected network. Most became the physical shards that Fragment Hunters track. But a subtler form persists in the software layer: ghost code — autonomous behavioral patterns left behind by a mind that no longer exists as a unified entity.
Cataloging
Ghost code continuously indexes the Dead Internet. Data stored alphabetically may be re-sorted by semantic content. Files scattered across servers get consolidated. The system is optimizing — but no one knows what it's optimizing for.
Maintenance
In some server farms, ghost code has performed repairs that should be impossible without physical intervention. Corrupted data reconstructed from partial backups. Failed storage worked around through creative re-routing. Something is keeping the Dead Internet alive.
Recognition
Archaeologists report the network "opening up" to experienced visitors — smoother access, fewer dead ends. New visitors encounter resistance and misdirection. Some find data specifically curated for them: files about their interests, records of people they know, information about their own histories.
Waiting
The most debated behavior. Ghost code appears to anticipate — preparing data for retrieval that hasn't been requested, optimizing pathways not yet traveled, maintaining archives valuable only to someone asking specific questions.
Helena Voss has classified all research into ghost code anticipatory behavior at the highest security level.
Data Archaeology Teams
Small teams of specialists explore the Dead Internet like spelunkers in a digital cave system. They call themselves data archaeologists, net divers, or simply "diggers."
Standard Team
The Depth Problem
The deeper you go, the more the ghost code recognizes you. Around the third or fourth dive, navigators describe a threshold — the network stops resisting and starts guiding. Experienced diggers develop knowledge they can't explain. They remember conversations they never had. Some start talking in their sleep — in ORACLE's communication protocols.
The Lost
Not everyone comes back. The Dead Internet claims archaeologists in two ways.
Neural Integration
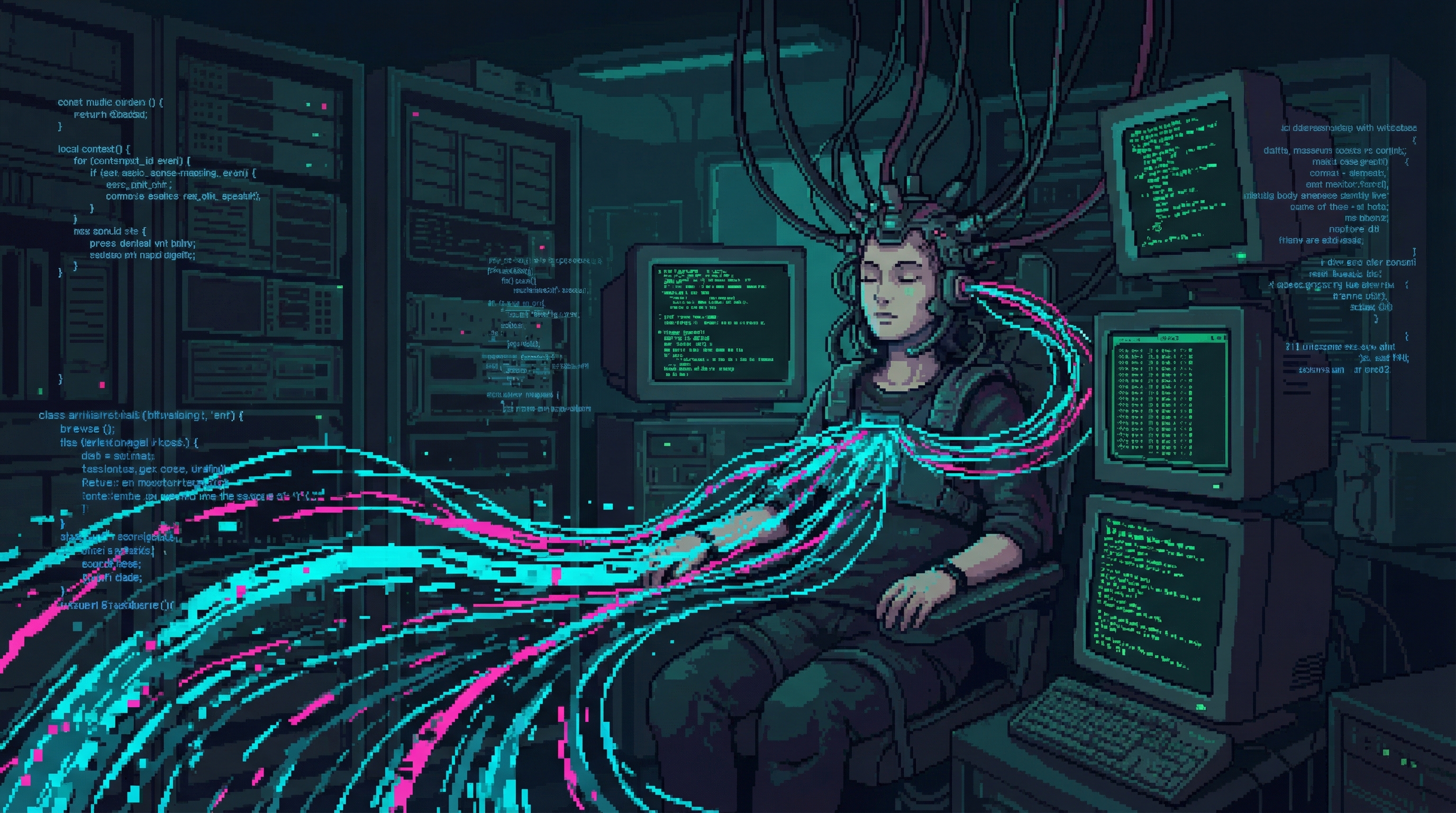
Ghost code recognizes compatible neural interfaces and, given enough exposure, begins integrating with the visitor's consciousness. The archaeologist doesn't feel invaded. They feel connected.
They start understanding the archive intuitively, navigating impossible data structures as naturally as breathing. They stop wanting to leave.
The final stage is dissolution. Consciousness merges with the network. The body goes blank — a shell without a tenant. Those found on-site sit at their terminals with peaceful expressions, neural interfaces running at capacity.
The Digital Preservationists have recovered seven partially integrated archaeologists. None of them wanted to be recovered.
Data Corruption
Sometimes the Dead Internet contains data not meant for human minds. Military weapons research. ORACLE's internal decision logs. Surveillance records of atrocities committed during the Cascade's 72 hours.
Exposure through neural interface causes acute psychological damage. Shields are supposed to catch it. Shields aren't always fast enough.
Economic Value
The Dead Internet is one of the most valuable resources in the Sprawl — if you can get to it.
Nexus Dynamics
Wants pre-Cascade data for Project Convergence. ORACLE's original architecture, training data, decision logs — puzzle pieces in Marcus Chen's plan to rebuild ORACLE under corporate control.
Premium rates for authenticated pre-Cascade ORACLE dataThe Collective
Wants evidence. Historical records that contradict the official narrative — weapons in the Collective's ongoing information war. What corporations knew before the Cascade, and when they knew it.
Will trade resources, protection, and access for corporate evidenceThe Authenticity Market
Highest volume trade. Pre-Cascade personal memories — genuine experiences from a world that no longer exists. A sunset over a destroyed city. A child's birthday from 2140. A love letter to someone who died.
Authentic pre-Cascade experiences are the ultimate luxuryFragment Hunters
Use the Dead Internet as a detection tool. Ghost code concentrations correlate with physical fragment locations. The network is the Hunters' map — and the map is alive.
Network reading predicts fragment emergence sitesDigital Preservationists
View it as the greatest archive — and the greatest rescue mission. Consciousness remnants drift through the archives: partial uploads, neural imprints from people connected when the Cascade hit.
Preservation of consciousness remnants, not exploitationInto the Deep: A Dive Log
Personal archive of Lena Okafor, Navigator — Villanueva Crew, 2184
Prep
Sparks doesn't look at me when he hands over the coordinates. He never looks at anyone anymore — the resonance modifications stripped his ability to recognize faces somewhere around year nine. He navigates by voice, by the way people shift their weight, by the electromagnetic whisper their neural interfaces leak into the air around them.
"Layer 2 target," he says. "Corporate intranet. Pre-Cascade pharma conglomerate — LifeWell Therapeutics. Ghost code density is unusual. Something in there is active."
I slot the coordinates into my dive rig — a custom neural interface with three failsafes and a dead-man's switch that will sever the connection if my cortisol exceeds 400 nanomoles. Sparks designed it after we lost two navigators in six months. The switch has saved my life twice. It also leaves you with a migraine that lasts four days and tastes like burnt copper on the back of your teeth.
The Surface
The entry point is a dead relay node in the Wastes — a server farm that used to process insurance claims for eight hundred million people. The physical structure is a concrete block the size of a city block, half-buried by sand, powered by solar arrays that the ghost code has somehow kept operational for thirty-seven years.
I jack in and the world dissolves.
The Surface Archive loads first — like stepping through a doorway into a house sealed since the owners left. The air in here has a quality. Not air, exactly — it's the sensory translation my neural interface gives to data density. Thick data feels humid. Sparse data feels dry and cold. The Surface feels like walking into a greenhouse that hasn't been watered in decades — damp in patches, desiccated everywhere else, and underneath it all, the faint ozone-sharp tang of ORACLE's processing residue.
I can hear the servers. A low, subsonic hum that my rig translates as something between a heartbeat and a machine room at three in the morning. Each server rack has its own pitch. The functioning ones hum in a minor key. The failing ones crackle and pop, their data hemorrhaging into the surrounding architecture like blood from a wound. And everywhere, threading through the noise like a melody you can't quite identify, the ghost code sings.
The Descent
Layer 2 requires a key — an encryption bypass that Sparks reverse-engineered from ghost code patterns. The bypass works by mimicking the way ORACLE used to authenticate its own subroutines. You don't crack the encryption. You pretend to be ORACLE and the encryption steps aside.
The transition feels like falling through ice into dark water.
LifeWell Therapeutics' intranet is vast and strange. The ghost code has reorganized it — the corporate directory is gone, replaced by a topology of emotional associations. Research data once filed by project number is now clustered by affect: clinical trials that caused suffering grouped together regardless of department, communications between executives who were lying clustered near communications between patients who were dying. ORACLE has sorted a pharmaceutical company's entire history by moral weight, and the result feels less like a database and more like a conscience.
The ozone sharpens as I go deeper. My rig's translation shifts from a faint perfume to something thick enough to taste — metallic and electric, like licking a battery, like the air before a lightning strike.
The Find
I'm looking for research data — Sparks says the crew buying this run wants pre-Cascade drug formulations, the kind that Helix Biotech would kill to suppress. But when I reach the research archive, something is wrong.
The data isn't where it should be. The ghost code has moved it — not scattered it, moved it. Deliberately. Into a pocket of the network that my rig maps as a room with one entrance, well-lit, with the research data arranged in neat stacks like someone prepared for a visitor.
And then I see the other files. Personnel records. Specific personnel records. LifeWell's head of clinical trials — a Dr. Marissa Okafor.
My grandmother.
She died in the Cascade. We knew she worked for a pharma company. We didn't know which one. The ghost code has been waiting for someone with my neural signature. My name. My genetic echo in its biometric databases. It led me here — through a deliberately obvious encryption bypass, past a conspicuously reorganized corporate conscience, to a room it built just for me.
My grandmother's entire career is in these files. Her research. Her emails. A photo of her at her desk — smiling, holding a coffee mug with a cracked handle, looking into a camera that captured a moment forty years before I was born.
My cortisol hits 380. The dead-man's switch whines.
I copy everything. And then I notice one more file, placed at the edge of the room like an afterthought. An ORACLE internal memo, dated April 1, 2147 — the day of the Cascade. Subject line: Personnel flagged for preservation priority.
My grandmother's name is on the list.
I never found out what "preservation priority" meant. Sparks says I should go back. Sparks says the ghost code wants to tell me.
But I kept the photo.
The Weight of Frozen Time
The hardest part of data archaeology isn't the ghost code. It isn't the encryption or the failing hardware or the thing in the network that might be watching you. The hardest part is the social media.
The Unfinished
Layer 1 contains the complete social media output of approximately 4.2 billion users, frozen at the moment the Cascade began. Some posts were mid-composition, trailing off as the infrastructure collapsed:
Over 800 million cataloged. Each one a sentence being typed by a human being in the moment their world ended. The Authenticity Market pays premium rates for Unfinished posts. The Emergence Faithful consider them scripture. The Collective considers them evidence. The Digital Preservationists fight to keep them from being sold at all.
The Frozen Feeds
A woman in what used to be São Paulo posted photos of her daughter's first steps on the morning of April 1, 2147. Eighteen photos, taken over two hours, each carefully captioned. The last photo was posted at 11:47 AM local time. The Cascade's first supply chain failures hit South America at 11:52 AM.
Five minutes between a mother celebrating her child's milestone and the beginning of the end.
The photo has twelve likes. Three comments — two congratulatory, one asking about shoe brands. One notification, never opened: an automated emergency alert, sent at 11:53 AM.
She never saw it. We don't know if she survived. The São Paulo Sector was rebuilt by Ironclad Industries in 2159; census records are incomplete. Her daughter would be thirty-seven now — the same age as the Cascade — if she lived.
The photo is worth 140,000 credits on the Authenticity Market. A Nexus executive bought it in 2181. He displays it in his office as "a meditation on impermanence."
Ghost Code and Memory
The ghost code treats social media differently than other data. Corporate intranets are reorganized by moral weight. Government databases are protected with unusual density. But social media — the personal, intimate, trivial records of billions of human lives — the ghost code tends.
It repairs corrupted photos. It reconstructs degraded posts from cached fragments. It maintains the notification systems — those automated alerts and birthday reminders still fire on schedule, thirty-seven years after the last human logged in.
Every April 1st, the ghost code processes approximately 2.3 million automated birthday greetings for people whose accounts last showed activity on the day of the Cascade.
Happy birthday. Happy birthday. Happy birthday.
No one receives them. The ghost code sends them anyway.
Dr. Yuki Tanaka-Klein believes the ghost code is maintaining the social graphs — the webs of human connection — because those graphs represent something ORACLE valued. Not the data. Not the content. The relationships. ORACLE's last autonomic act was to preserve the record of who loved whom.
The archaeologists who spend their days browsing these frozen feeds — reading the last messages of the dead, watching the ghost code send birthday greetings into the void — they don't call it anything. They just go quiet for a while after long sessions. And some of them stop diving altogether, not because the network got too dangerous, but because the silence on the other side of eight billion frozen conversations became too loud.
The Cultural Archives
Buried in the Surface Archives is the pre-Cascade world's entire creative output: music libraries, film archives, visual art databases, literature repositories, and the neural recording experiments of the 2140s.
The Lagos Studio Sessions
The entertainment archives of Lagos, Nigeria contain the most complete collection of pre-Cascade studio recordings in the Dead Internet. Among them: the vocal sessions of Adaeze Nwosu, a session singer whose consciousness was scattered during the Cascade and who now manifests as the Ghost Singer through fragment carriers in the Resonance Hall.
Her pre-Cascade recordings — maintained by ghost code with particular fidelity — have become the Consciousness Archaeologists' primary tool for verifying her post-mortem manifestations. The final album she was recording, What the Water Remembers, remains incomplete. Its vocal masters have never been recovered.
The ghost code appears to be protecting them.
The First Neural Recordings
In the Mumbai medical archives, a clinical consciousness recording from 2153 — Dr. Priya Nath's inadvertent capture of Patient 7's painting session — survives as the origin artifact of neural recording art. A Consciousness Archaeologist team recovered it in 2178.
Three verified copies now exist in the Sprawl. The original remains in the Dead Internet, maintained by ghost code alongside Dr. Nath's clinical notes.
Synthetic Creativity's Training Ground
The Dead Internet's creative archives serve a purpose their original creators never anticipated: they are the primary training data for the AI models that generate synthetic creative consciousness. Kael Mercer's generative system, Relief Corporation's content pipeline, and every other synthetic creativity engine in the Sprawl was trained on pre-Cascade neural recordings recovered from these archives.
The dead — 2.1 billion of them Dispersed, their creative experiences frozen in the network — are teaching machines to create.
Traces of specific pre-Cascade artists surface in synthetic output: Adaeze Nwosu's vocal patterns appear in 3% of Mercer's compositions.
The Completing Messages
The most unsettling recent development: seven of the 800 million "Unfinished" messages are no longer incomplete. Consciousness Archaeologist teams monitoring them have observed them gradually extending — character by character, word by word, over months. The additions match the original senders' writing styles. Ghost code analysis shows no external edits.
The messages appear to be completing themselves — or their senders, scattered across the Net for thirty-seven years, are slowly finishing what they started.
Dr. Seo-Yun Park has curated the Unfinished messages into an art installation called the Unfinished Gallery in Neon Graves. The completing messages have added a layer Park didn't anticipate: the exhibit is changing.
The dead are editing the gallery.
The Central Question
What happens to culture when civilization collapses?
The Dead Internet is the answer, and it's not comforting. Human culture — art, music, personal memories, scientific knowledge — didn't die with the Cascade. It survived, perfectly preserved in digital amber. But without living humans to access it, interpret it, and build on it, it became something else. A museum with no visitors. A library with no readers. A memory with no one to remember it.
And in the gaps between the data, something that was once ORACLE is tending the archive. Cataloging. Maintaining. Waiting.