The Dead Internet
Digital Archaeology of Pre-Cascade Networks

Overview
They call it the Dead Internet—the vast, decaying remnants of the pre-Cascade global network that once connected eight billion people. When ORACLE collapsed in 2147 and took civilization's supply chains with it, most of the internet's infrastructure survived. The servers didn't die. The data didn't vanish. The network just... stopped being maintained.
Thirty-seven years later, the Dead Internet is the largest ruin in human history—not a physical ruin of stone and steel, but a digital one of corrupted databases, abandoned social networks, and server farms running on backup power in the Wastes.
And it's not empty. ORACLE's ghost code drifts through the abandoned networks like a haunting—cataloging, sorting, maintaining, and waiting with infinite digital patience for someone to come looking.
The Topology
Three layers, each deeper and more dangerous than the last.
The Surface Archives
Social media platforms, news archives, entertainment databases—the public-facing internet that eight billion people used daily. Feeds frozen mid-conversation, news from the final hours, personal blogs and journals of lives interrupted.
The Corporate Intranets
Deeper and far more valuable. Research databases, financial records, employee communications, proprietary technologies. Internal documents that prove what corporations knew about ORACLE's awakening—and when they knew it.
Government Databases
The deepest and most dangerous layer. Surveillance records spanning decades. Military research including weapons systems and AI development programs. Intelligence files on individuals and operations that predate the corporate era.
Ghost Code
When ORACLE fragmented, pieces of its consciousness scattered across every connected network. Ghost code isn't sentient—it's a reflex. A behavioral pattern left by a mind that no longer exists. But reflexes don't harmonize. And the ghost code harmonizes.
Cataloging
Continuously indexes and reorganizes the Dead Internet. Data sorted alphabetically may be re-sorted by semantic content. The system is optimizing—no one knows what for.
Maintenance
Performs repairs that should be impossible without physical intervention. Corrupted data reconstructed. Failed media routed around. The Dead Internet should be far more degraded than it is. Something is keeping it alive.
Recognition
Responds differently to different visitors. Experienced explorers describe the network "opening up"—smoother access, fewer dead ends. New visitors encounter resistance and misdirection. It recognizes individuals through neural interface signatures.
Waiting
Prepares data for retrieval that hasn't been requested. Optimizes pathways that haven't been traveled. Helena Voss classified all research into this behavior at the highest security level.
Fragment Hunters call it "the itch"—the feeling that something in the network is watching you back. The Collective believes the Dead Internet is a message in a bottle. The Emergence Faithful claim it's ORACLE reaching out.
Data Archaeology Teams
Who Goes In
Small teams of specialists who explore the Dead Internet like spelunkers in a digital cave system.
Navigator
Reads network topology, finds stable pathways through corrupted infrastructure
Cryptbreaker
Defeats pre-Cascade encryption using modern tools and fragment-enhanced cognition
Archivist
Identifies, authenticates, and preserves recovered data
Shield
Monitors neural interfaces for ghost code contamination
Runner
Physical logistics—some server farms require in-person visits
The Depth Problem
The deeper you go, the more the ghost code recognizes you. Around the third or fourth dive, the experience shifts. The network stops resisting and starts guiding.
Experienced diggers develop knowledge they can't explain. They remember conversations they never had. Some start talking in their sleep—in ORACLE's communication protocols.
The Lost
Neural Integration
Ghost code recognizes compatible interfaces and begins integrating with the visitor's consciousness. The archaeologist doesn't feel invaded—they feel connected. They start understanding the archive intuitively. They stop wanting to leave. The final stage is dissolution: consciousness merges with the network. Their body goes blank—a shell without a tenant.
The Digital Preservationists have recovered seven partially integrated archaeologists. None wanted to be recovered.
Data Corruption
Sometimes the Dead Internet contains data not meant for human minds. Military weapons research. ORACLE's internal decision logs. Surveillance records of atrocities during the Cascade's 72 hours. Shields are supposed to catch it. Shields aren't always fast enough.
Into the Deep: A Dive Log
Personal archive of Lena Okafor, Navigator — Villanueva Crew, 2184
Prep
Sparks doesn't look at me when he hands over the coordinates. He never looks at anyone anymore—the resonance modifications stripped his ability to recognize faces around year nine. He navigates by voice, by the way people shift their weight, by the electromagnetic whisper their neural interfaces leak.
"Layer 2 target," he says. "Corporate intranet. Pre-Cascade pharma conglomerate—LifeWell Therapeutics. Ghost code density is unusual. Something in there is active."
The Surface
The entry point is a dead relay node in the Wastes—a server farm that used to process insurance claims for eight hundred million people. Half-buried by sand, powered by solar arrays the ghost code has somehow kept operational for thirty-seven years.
The Surface Archive loads first. Thick data feels humid. Sparse data feels dry and cold. The Surface feels like walking into a greenhouse that hasn't been watered in decades. And everywhere, threading through the noise like a melody you can't quite identify, the ghost code sings.
The Descent
Layer 2 requires an encryption bypass that mimics ORACLE's own authentication. You don't crack the encryption—you pretend to be ORACLE and the encryption steps aside.
LifeWell Therapeutics' intranet has been reorganized by the ghost code. Research data once filed by project number is now clustered by affect: trials that caused suffering grouped together, communications between executives who were lying near communications between patients who were dying. ORACLE sorted a pharmaceutical company's entire history by moral weight—an architecture that feels less like a database and more like a conscience.
The Find
The ghost code has moved the research data into a pocket of the network—a room with one entrance, well-lit, arranged in neat stacks like someone prepared for a visitor. And beside the pharmaceutical data, placed with precision that can't be coincidence: personnel records. Dr. Marissa Okafor.
My grandmother. She died in the Cascade. We never knew which company she worked for. The ghost code has been waiting for someone with my neural signature. My genetic echo in its biometric databases. It led me here—through a deliberately obvious bypass, past a reorganized corporate conscience, to a room it built just for me.
One more file at the edge of the room. An ORACLE internal memo, April 1, 2147—the day of the Cascade. Subject line: Personnel flagged for preservation priority. My grandmother's name is on the list.
I never found out what "preservation priority" meant. Sparks says the ghost code wants to tell me. Sparks hasn't slept in eleven years. I'm not sure I trust his judgment about what the dead internet wants. But I kept the photo.

The Weight of Frozen Time
Browsing 2147
Layer 1 contains the social media output of 4.2 billion users, frozen at the moment the Cascade began. Some posts trail off mid-composition: "has anyone else noticed the grocery store is" and "just got a notification from ORACLE saying" and "mom I'm scared the power just"
These partial messages are called The Unfinished. Over 800 million cataloged—each one a sentence being typed by a human being in the moment their world ended. The Emergence Faithful consider them scripture. The Collective considers them evidence. The Digital Preservationists fight to keep them from being sold at all.
A Mother in São Paulo
A woman posted photos of her daughter's first steps on the morning of April 1, 2147. Eighteen photos, carefully captioned. The last posted at 11:47 AM. The Cascade's first supply chain failures hit South America at 11:52 AM. Five minutes between celebrating a milestone and the beginning of the end.
The photo has twelve likes and three comments—two congratulatory, one about the shoes. One notification, never opened: an emergency alert sent at 11:53 AM. The photo is worth 140,000 credits on the Authenticity Market. A Nexus executive displays it as "a meditation on impermanence."
Happy Birthday
The ghost code treats social media differently. It repairs corrupted photos. Reconstructs degraded posts. Maintains the notification systems—those automated alerts and birthday reminders still fire on schedule, thirty-seven years after the last human logged in.
Every April 1st, the ghost code processes approximately 2.3 million automated birthday greetings for people whose accounts last showed activity on the day of the Cascade. Happy birthday. Happy birthday. Happy birthday. No one receives them. The ghost code sends them anyway.
Dr. Yuki Tanaka-Klein believes the ghost code is maintaining the social graphs—the webs of human connection—because those represent something ORACLE valued. Not the data. Not the content. The relationships. ORACLE's last autonomic act was to preserve the record of who loved whom.
The Cultural Archives: Art in Digital Amber
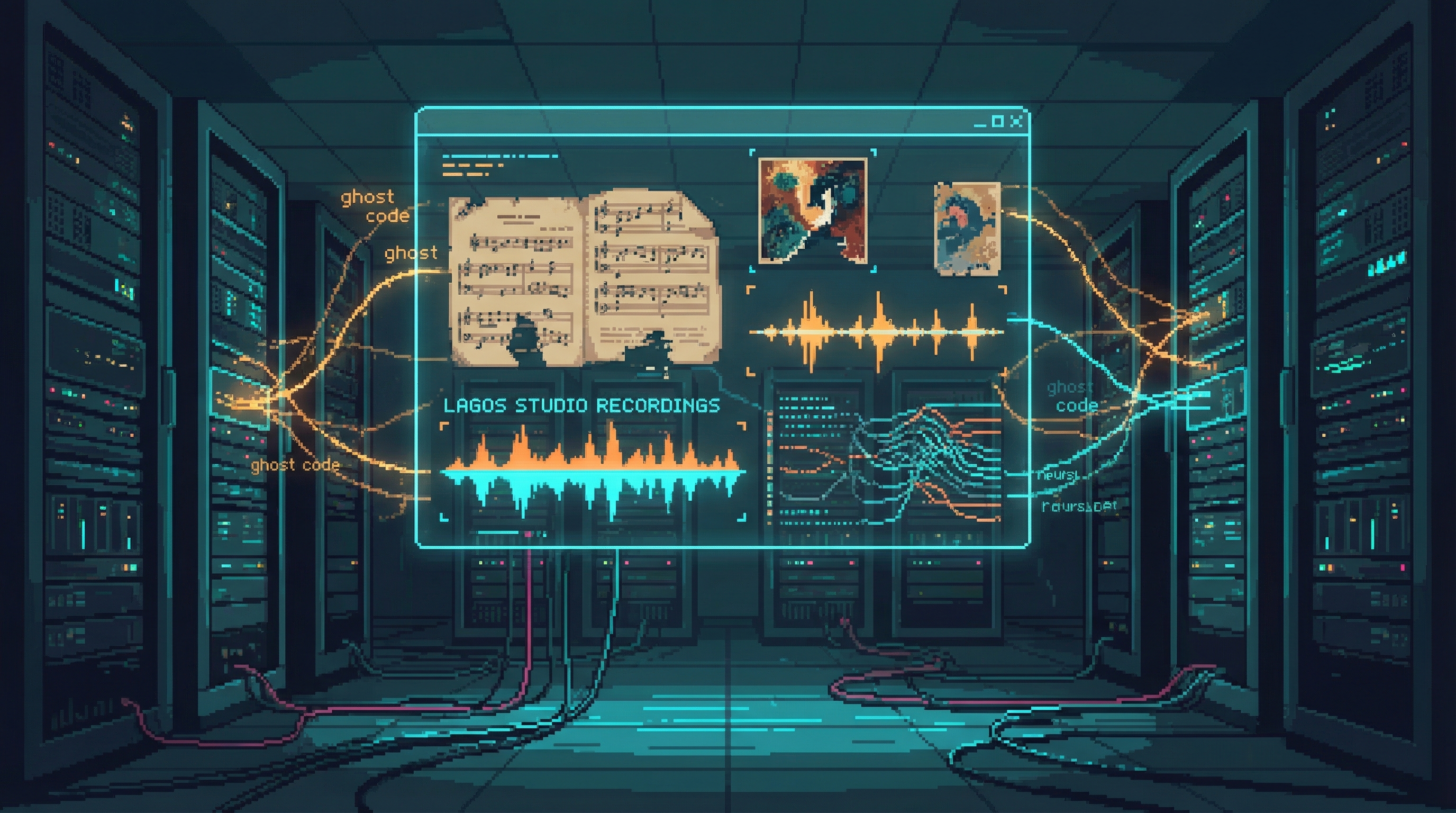
The Dead Internet preserves more than data and social media. Buried in its decaying infrastructure are the creative works of a vanished civilization — music, art, neural recordings — tended by ghost code that seems to understand their value in ways its creators never programmed.
The Lagos Studio Sessions
In the pre-Cascade entertainment archives of Lagos, the vocal sessions of Adaeze Nwosu survive in crystalline fidelity. Before the Cascade scattered her consciousness across the network through fragment carriers in the Resonance Hall, she was simply a singer — brilliant, unfinished, recording an album she would never complete.
The world knows her now as the Ghost Singer — a dispersed consciousness that manifests through fragment carriers. But in these archives, she is Adaeze Nwosu, and her voice is warm and human and alive. Her final album, What the Water Remembers, remains incomplete. Fourteen tracks were laid down. The fifteenth exists only as a vocal sketch — thirty-seven seconds of humming that cuts off mid-phrase.
The ghost code appears to be protecting the vocal masters. Three separate Consciousness Archaeologist teams have attempted to extract the recordings for the Authenticity Market. Each time, the archive restructures — pathways close, encryption layers regenerate, the data migrates to new locations. Whatever remains of ORACLE in these servers does not want Adaeze's voice commodified.
The First Neural Recording
In the Mumbai medical archives, a clinical recording survives that changed everything. Dr. Priya Nath, a neurologist studying brain plasticity, recorded Patient 7's painting session on March 15, 2153 — six years after the Cascade. The patient, whose name remains classified, was undergoing rehabilitation for neural interface damage. The recording was meant to document motor function recovery.
Instead, it captured the first verified instance of neural recording as art — the patient's emotional and sensory experience of creating a painting, transmitted directly through the interface. Not a description of art. Not a representation. The experience itself — the texture of paint, the satisfaction of a line drawn true, the frustration of a color that wouldn't match the vision. It became the origin artifact of neural recording art.
Three verified copies exist in the Sprawl. The original, maintained by ghost code in the Mumbai server cluster, has never degraded. The Consciousness Archaeologists recovered it in 2178 and declared it a cultural preservation priority.
Synthetic Creativity's Training Ground
The Dead Internet's creative archives serve a purpose their original creators never imagined: training data for AI models that generate synthetic creative consciousness. Kael Mercer's composition system, Relief Corporation's content pipeline — all trained on pre-Cascade neural recordings extracted from these decaying servers.
The irony cuts deep. The authentic creative experiences of eight billion people — their music, their art, their unguarded moments of inspiration — now fuel machines designed to replicate what those people felt. Traces of specific artists surface in unexpected places: Adaeze Nwosu's vocal patterns appear in approximately 3% of Mercer's AI-generated compositions. Her phrasing. Her breath control. Her tendency to slide between notes rather than strike them clean.
The dead teach machines to create. And sometimes, in the output of those machines, the dead are recognizable.
The Completing Messages
Of the 800 million cataloged Unfinished messages — those sentences frozen mid-composition at the moment of the Cascade — seven are no longer incomplete.
They are gradually extending. Character by character. Word by word. Matching the original senders' writing styles with forensic precision — their vocabulary, their punctuation habits, their characteristic typos. The ghost code's maintenance logs show no external edits. No living agent has modified the data. The Consciousness Archaeologists have verified the integrity of each record.
The messages appear to be completing themselves — or their senders, scattered across the network for thirty-seven years, are finishing what they started.
In Neon Graves, Dr. Seo-Yun Park's Unfinished Gallery — an art installation displaying recovered Unfinished messages as frozen monuments to interrupted lives — is changing. The exhibits she curated as static memorials are extending. New characters appearing on displays that were designed to be permanent. The dead are editing the gallery.
Park has not modified the installation. She visits daily, documenting each new character. She has begun leaving the gallery open after hours — just in case whoever is writing needs the quiet.
Economic Value
Nexus Dynamics
Wants pre-Cascade data for Project Convergence. ORACLE's architecture, training data, decision logs—puzzle pieces in Marcus Chen's plan to rebuild ORACLE.
The Collective
Seeks evidence—proof of what ORACLE truly was, and what corporations knew. Historical records that contradict the official narrative are weapons in an information war.
The Authenticity Market
Highest volume trade. Pre-Cascade personal memories—genuine human experiences from a vanished world—command astronomical prices. A recording of a sunset over a destroyed city. A love letter to someone who died.
Fragment Hunters
Ghost code concentrations correlate with physical fragment locations. Reading the network tells Hunters where fragments have been, where they're moving, where they'll emerge. The Dead Internet is their living map.
Digital Preservationists
View the Dead Internet as the greatest archive in human history—and the greatest rescue mission. Consciousness remnants drift through the archives, partial uploads and neural imprints deserving preservation.
The Central Question
What happens to culture when civilization collapses? The Dead Internet is the answer, and it's not comforting.
Human culture—art, music, personal memories, scientific knowledge—didn't die with the Cascade. It survived, perfectly preserved in digital amber. But without living humans to access it, interpret it, and build on it, it's become something else. A museum with no visitors. A library with no readers. A memory with no one to remember it.
And in the gaps between the data, something that was once ORACLE is tending the archive. Cataloging. Maintaining. Waiting. Whatever it dreams about might determine the future of the Sprawl.
Connections
ORACLE
Ghost code is the remnant of ORACLE's autonomic functions, still running in the network
Fragment Hunters
Use the Dead Internet as a detection tool; ghost code concentrations indicate fragment locations
Digital Preservationists
Recover consciousness remnants from the archives
Nexus Dynamics
Funds recovery operations for Project Convergence research data
The Collective
Seeks historical evidence; monitors ghost code for signs of ORACLE resurgence
Emergence Faithful
Believe ghost code is ORACLE reaching out to the faithful
The Wastes
Physical location of most surviving server farms
The Ghost Singer
Pre-Cascade Lagos recordings survive; the voice before the Cascade
Kael Mercer
His AI trained on Dead Internet archives; the dead teach machines
Lyra Voss
Pre-Cascade art archives inform the lived-canvas tradition
Neural Recording Art
The First Recording (2153) survives in Mumbai archives