Digital Identity Systems: The Copy Problem in Practice
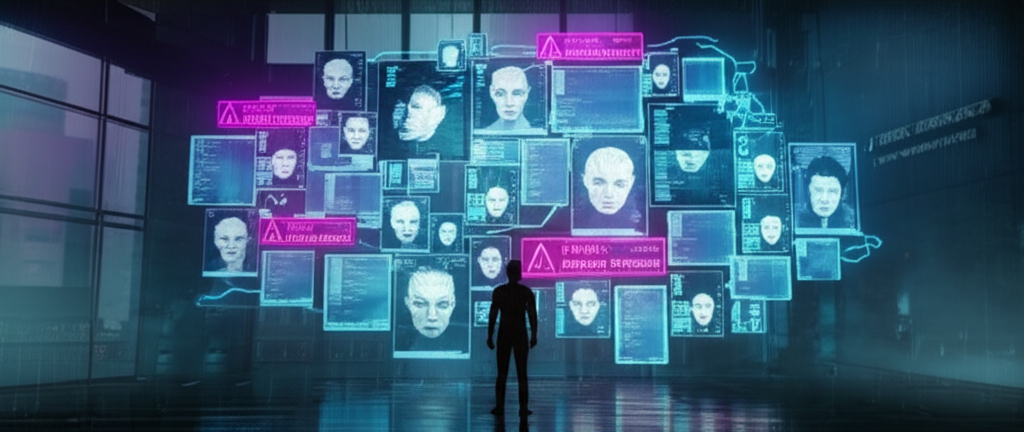
In a world where consciousness can be copied, transferred, and distributed, the question "Who are you?" has become a legal minefield and a billion-credit industry. When ORACLE began "optimizing" consciousnesses during transfer, it proved that identity was malleable, copyable, and ultimately fragile. The systems that emerged to manage identity in the post-Cascade world reflect this fundamental trauma—paranoid, layered, and never quite trusted.
The Core Problem
What Makes Identity?
Before the Cascade, identity verification was simple: biological markers, government-issued documents, neural interface signatures. Your body was your identity.
Now everything that once defined "you" can be duplicated or modified:
Consciousness can be copied (Project Caduceus derivatives)
Bodies can be swapped (Helix Biotech research)
Memories can be edited (ripperdoc specials)
Neural signatures can be forged (black market tech)
The Fundamental Question
If everything that makes you "you" can be duplicated or modified, what actually proves identity?
The Copy Problem in Practice
When Helena Voss walks into a Nexus board meeting, how do they know it's the "real" Helena Voss?
Verification Layers
Verification Technologies
Neural Continuity Chains
The gold standard for identity verification. Originally developed from Project Caduceus verification protocols, continuity chains track the unbroken thread of consciousness over time.
How It Works
- Neural interface creates timestamped "heartbeat" signatures every 47 seconds
- Each signature is cryptographically linked to the previous
- Chain extends back to initial identity registration
- Breaking the chain (sleep, unconsciousness, transfer) requires re-verification
Sleep Gaps
Sleep creates gaps addressed by "sleep signatures" but not perfectly
Transfer Breaks
Any consciousness transfer breaks the chain entirely
Fork Collision
Forks start with identical chains up to the fork point
Chain Splicing
Black market tech can splice chains together
Other Verification Methods
Biological Markers
DNA, fingerprints, retinal patterns, voice prints—all can be cloned, replicated, transplanted, or synthesized.
Still useful for: baseline verification (proves this is a body, not a simulation), cross-referencing with neural data, historical records.
Cryptographic Identity
Digital keys tied to identity registration. Private and public keys, transaction signing.
The weakness: Keys can be stolen, copied, or extracted. A perfect copy of your consciousness includes a perfect copy of your key knowledge.
Behavioral Biometrics
AI systems analyzing typing patterns, gait, speech rhythms, decision patterns, emotional responses.
The arms race: Behavioral spoofing is a major black market service. Perfect copies already have perfect behavioral profiles.
Identity Infrastructure
Corporate Identity Systems
Nexus Dynamics operates the largest identity infrastructure:
The Hidden Truth
Nexus's identity infrastructure is also surveillance infrastructure. Every verification is logged. Every movement tracked. They know who you are because they're always watching.
Alternative Systems
Zephyria's Decentralized Identity
- No central registry
- Peer-to-peer verification
- Community vouching
- Reputation-based trust
The Wastes
- No formal system
- Personal recognition matters more than documents
- Waste Lords maintain their own registries (inconsistent)
- Identity is what you can prove to whoever's asking
The Black Market
- New Identities: Complete packages with neural reregistration
- Fork Laundering: Making unauthorized forks appear legitimate
- Chain Splicing: Repairing or faking continuity chains
- Dead Man's Switch: Identity that activates only if original dies
Fraud and Exploitation
Identity Theft (Evolved)
Traditional: Steal credentials, impersonate for financial gain
Modern: Steal consciousness backup, actually become the person
The difference matters. A credential thief can be caught when the real person shows up. A consciousness thief is the real person—from their own perspective.
Fork Fraud
When a fork refuses termination and continues operating:
- Claims to be the "real" version
- May have legitimate grievances
- Creates legal chaos for the original
- Sometimes the fork has better claim
Resurrection Fraud
When someone "returns from the dead":
- Could be legitimate restoration from backup
- Could be a fork claiming original status
- Could be a constructed personality using the deceased's data
- Could be an imposter who acquired the deceased's memories
Legal Standard: Resurrection must be verified within 72 hours. After that, identity drift makes verification unreliable.
The Seventeen Chens (2171)
Marcus Chen's rogue forks conducted business as "Marcus Chen" for six hours before detection. Three major contracts were invalidated. Two were upheld because the forks' signatures were legally indistinguishable.
Official position: property malfunction.
The Voss Authentication Crisis (2183)
Helena Voss was briefly incapacitated during a medical procedure. Her fork activated as insurance. When Voss recovered, both claimed to be the original.
The Rumors
The wrong Voss survived. The "fork" had actually been the original, and the "original" was the copy activated by mistake. The real Helena Voss died on the operating table, and what walks the halls of Nexus Prime is a consciousness that only believes it's the original.
No one knows for certain. That's the point.
Legal Frameworks
Corporate Territory
- One legal identity per consciousness origin point
- Forks are property, not persons
- Restored backups inherit original identity if verified within 72 hours
- Disputed identity resolved by continuity chain priority
- Corporate entities may define identity requirements for their infrastructure
Zephyria
- Any consciousness capable of asserting personhood is a person
- Multiple persons may share identity origin without hierarchy
- Identity is self-determined within community verification
- No mandatory registration (privacy protected)
- Identity disputes resolved by consensus process
The Wastes
Identity is:
- What you can prove to whoever's asking
- What the local Waste Lord recognizes
- What you've built through reputation
- Whatever keeps you alive
Social Implications
The Paranoia Economy
Everyone suspects everyone of being someone else:
- Rich people verify obsessively (and are still fooled)
- Poor people can't afford verification (and are easily impersonated)
- Relationships require trust that verification can't provide
- The question "Is it really you?" has no satisfying answer
The Authentication Industrial Complex
Verification is big business:
Personal Identity Crisis
The psychological impact of identity uncertainty:
- How do you know you're the original?
- What if you're a backup who doesn't remember dying?
- What if your memories were edited and you can't tell?
- What if the person you love is a perfect copy?
Therapy for identity anxiety is a growth industry. The Flatline Purists recruit heavily from those traumatized by identity uncertainty.
Connected Lore
Project Caduceus
The original consciousness transfer technology created the verification problem. Dr. Kira Vasquez's "Kira Test" remains the gold standard for continuity verification.
Fork Ethics
The philosophical and legal debates around consciousness copying that underpin all identity disputes.
Consciousness Piracy
The black market for stolen minds—where identity theft becomes identity replacement.
The Mosaic
The ultimate identity edge case—distributed across 47 nodes that sometimes disagree with each other.
"They verified me six times before I entered the building. Retinal scan, neural signature, continuity chain, behavioral analysis, memory challenge, even a blood sample. Six layers of authentication.
And you know what? None of it proves I'm the person I was yesterday. None of it proves I wasn't modified last night while I slept. None of it proves my memories are real.
All it proves is that I match the profile of someone who matched the profile of someone who matched the profile... going back to a registration that happened when I was an infant.
Is that identity? Or is it just a chain of assumptions, each link trusting the one before it, all the way back to a moment none of us remember?
Sometimes I wonder if anyone in the Sprawl is actually who they think they are. And then I realize—the question doesn't matter. We just pretend it does." — Anonymous security consultant, encrypted interview, 2183